Integrate with PostgreSQL
EMQX supports integrating with PostgreSQL for password authentication.
TIP
Knowledge about basic EMQX authentication concepts
Data Schema and Query Statement
EMQX PostgreSQL authenticator supports almost any storage schema. You can determine how to store credentials and access them as your business needs, for example, using one or multiple tables, views, etc.
Users need to provide a query statement template and ensure the following fields are included:
password_hash: required; password (in plain text or hashed) stored in the database;salt: optional;salt = ""or just remove this field to indicate no salt value will be added;is_superuser: optional; flag if the current client is a superuser; default:false.
Example table structure for storing credentials:
CREATE TABLE mqtt_user (
id serial PRIMARY KEY,
username text NOT NULL UNIQUE,
password_hash text NOT NULL,
salt text NOT NULL,
is_superuser boolean DEFAULT false,
created timestamp with time zone DEFAULT NOW()
);TIP
The above example has created an implicit UNIQUE index field (username) that is helpful for the queries. When there is a significant number of users in the system, please optimize and index the tables to be queried beforehand to shorten the query response time and reduce the load for EMQX.
In this table, MQTT users are identified by username.
For example, if you want to add a document for a superuser (is_superuser: true) with username user123, password secret, and suffixed salt salt, the query statement should be:
INSERT INTO mqtt_user(username, password_hash, salt, is_superuser) VALUES ('user123', 'f84fa2149dbb62ed4e0cf1f550d2949b33a6513d3a7707e08502511c79ccb0ee', 'salt', true);
INSERT 0 1The corresponding configuration parameters are:
- password_hash_algorithm:
sha256 - salt_position:
suffix
SQL:
query = "SELECT password_hash, salt, is_superuser FROM mqtt_user WHERE username = ${username} LIMIT 1"Configure with Dashboard
You can use EMQX Dashboard to configure how to use PostgreSQL for password authentication.
- In EMQX Dashboard, click Access Control -> Authentication from the left navigation menu.
- On the Authentication page, click Create in the top right corner.
- Click to select Password-Based as Mechanism, and PostgreSQL as Backend to go to the Configuration tab, as shown below.
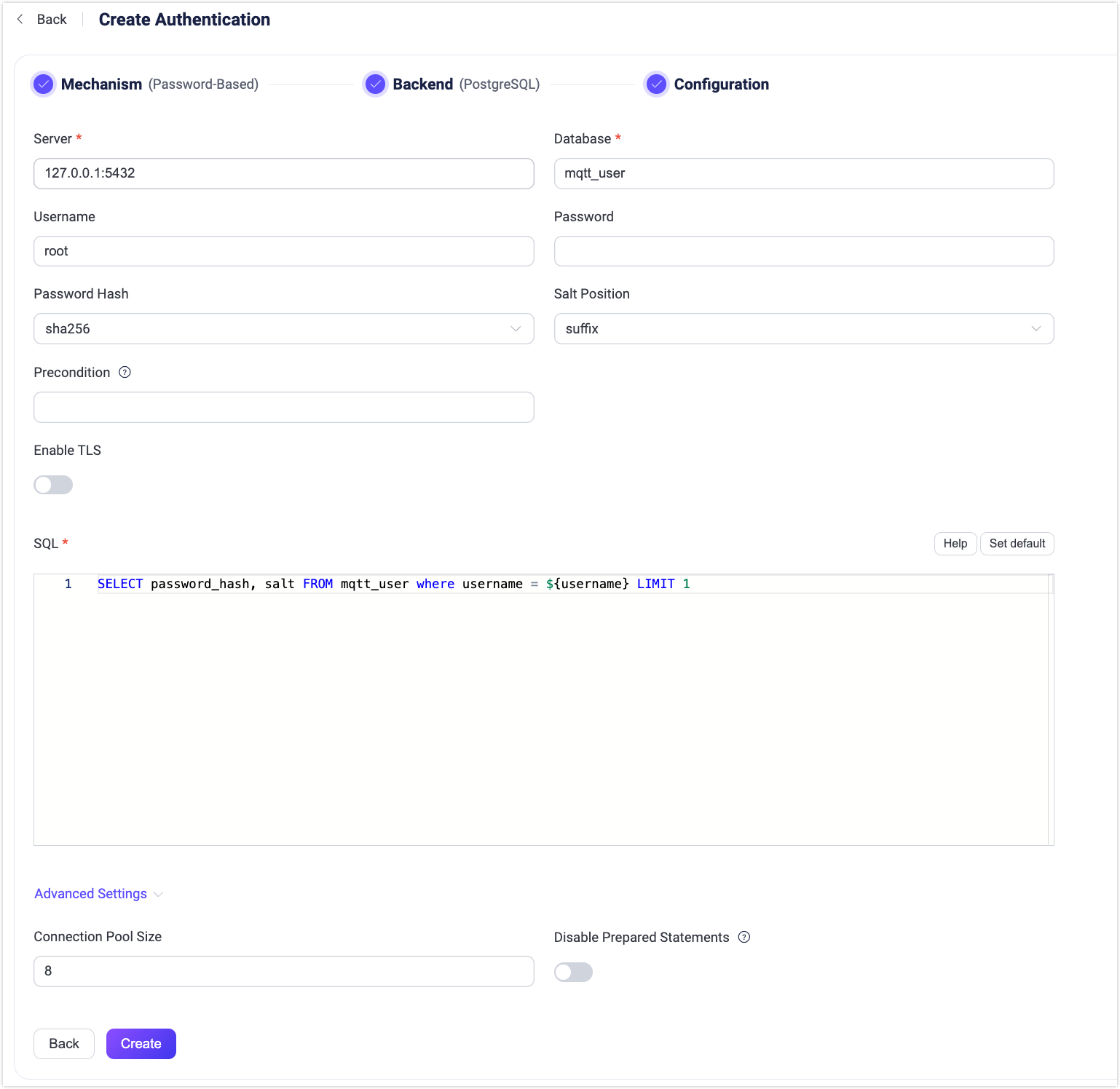
- Follow the instructions below to configure the authentication backend:
Enter the information for connecting to PostgreSQL.
- Server: Specify the server address that EMQX is to connect (
host:port). - Database: PostgreSQL database name.
- Username: Specify user name.
- Password: Specify user password.
- Server: Specify the server address that EMQX is to connect (
Configure settings related to authentication:
- Password Hash: Select the password hashing algorithm applied to plain-text passwords before results are stored in the database. Available options are
plain,md5,sha,sha256,sha512,bcrypt, andpbkdf2. Additional configurations depend on the selected algorithm:- For
md5,sha,sha256orsha512:- Salt Position: Determines how salt (random data) is mixed with the password. Options are
suffix,prefix, ordisable. You can keep the default value unless you migrate user credentials from external storage into the EMQX built-in database. - Resulting hash is represented as a string of hexadecimal characters, and compared case-insensitively with the stored credential.
- Salt Position: Determines how salt (random data) is mixed with the password. Options are
- For
plain:- Salt Position: should be
disable.
- Salt Position: should be
- For
bcrypt:- Salt Rounds: Defines the number of times the hash function is applied, expressed as 2Salt Rounds, also known as the "cost factor". The default value is
10, with a permissible range of5to10. A higher value is recommended for enhanced security. Note: Increasing the cost factor by 1 doubles the necessary time for authentication.
- Salt Rounds: Defines the number of times the hash function is applied, expressed as 2Salt Rounds, also known as the "cost factor". The default value is
- For
pbkdf2:- Pseudorandom Function: Selects the hash function that generates the key, such as
sha256. - Iteration Count: Sets the number of times the hash function is executed. The default is
4096. - Derived Key Length (optional): Specifies the length in bytes of the generated key. If left blank, the length will default to that determined by the selected pseudorandom function.
- Resulting hash is represented as a string of hexadecimal characters, and compared case-insensitively with the stored credential.
- Pseudorandom Function: Selects the hash function that generates the key, such as
- For
- Password Hash: Select the password hashing algorithm applied to plain-text passwords before results are stored in the database. Available options are
Precondition: A Variform expression used to control whether this PostgreSQL authenticator should be applied to a client connection. The expression is evaluated against attributes from the client (such as
username,clientid,listener, etc.). The authenticator will only be invoked if the expression evaluates to the string"true". Otherwise, it will be skipped. For more information about the precondition, see Authenticator Preconditions.Enable TLS: Turn on the toggle switch if you want to enable TLS. For more information on enabling TLS, see Network and TLS.
Advanced Settings: Configure connection pool, timeout, and prepared statement behavior.
- Connection Pool Size (optional): Specify the number of concurrent connections from an EMQX node to a PostgreSQL server. Default:
8. - Query Timeout (optional): Specify the waiting period before EMQX assumes the query has timed out. Units supported include milliseconds, second, minute, and hour. Default:
5seconds. - Connect Timeout (optional): Specify the waiting period before EMQX assumes the connection attempt has timed out. Units supported include milliseconds, second, minute, and hour. Default:
15seconds. - Disable Prepared Statements (optional): Disable the use of prepared statements for database queries. Enable this option if your PostgreSQL proxy or middleware (for example, PGBouncer or Supabase in Transaction mode) does not support session-level features such as prepared statements. Default: disabled.
- Connection Pool Size (optional): Specify the number of concurrent connections from an EMQX node to a PostgreSQL server. Default:
SQL: Fill in the query statement according to the data schema. For more information, see SQL data schema and query statement.
After you finish the settings, click Create.
Configure with Configuration Items
You can configure the EMQX PostgreSQL authenticator with EMQX configuration items. For a full list of configuration parameters, see the EMQX Enterprise Configuration Manual.
PostgreSQL authentication is identified with mechanism = password_based and backend = postgresql.
Sample configuration:
{
mechanism = password_based
backend = postgresql
password_hash_algorithm {
name = sha256
salt_position = suffix
}
database = mqtt
username = postgres
password = public
server = "127.0.0.1:5432"
query = "SELECT password_hash, salt, is_superuser FROM users where username = ${username} LIMIT 1"
query_timeout = "5s"
connect_timeout = "15s"
disable_prepared_statements = false
}